Pure devops: how the concept of "DevOps" emerged and developed. Part 2/2
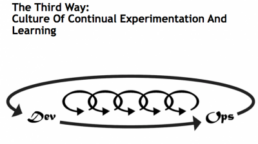
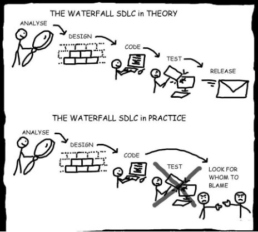
Serve and deliver Former Tripwire CTO Jin Kim in The Three Ways: The Principles…
Pure devops: how the concept of "DevOps" emerged and developed. Part 1/2
There are already thousands of controversies on the Internet about what DevOps…
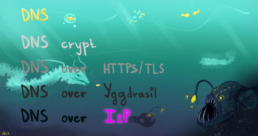
DNS over I2P - real privacy of DNS queries
Today it is difficult to surprise someone with the terms DoH (DNS over HTTPS),…
Automatic version number management with Azure DevOps
In this article, I'll walk you through how we set up a sequential…
5 approaches to cloud automation
How not to waste time and nerves on manual initialization and maintenance of…
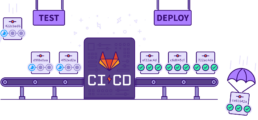
CI / CD Implementation for Enterprise Data Warehouses
There are many recipes for preparing CI / CDs on the Web for solving various…
Cloud cyber security: defining areas of responsibility and choosing a cloud provider
In this article, we will answer the following questions: Where is the border…